While today saw Paul Graham physically pass the reins to new Y Combinator president Sam Altman, the bigger buzz at Demo Day was about how most investors thought this was the best YC class yet. There were unsexy startups in industries ripe for disruption, deep B2B specialization to meet the needs of specific companies, and several non-profits out to make the world better, not themselves richer.
After Graham was awarded a pair of khaki shorts signed by the whole class, 68 startups took the stage at the Mountain View Computer History Museum. 55 presented on the record, and you can read about all of them in our overviews of Batch 1, Batch 2, and Batches 3 and 4. (If you want to be part of the next round of YC, the accelerator is currently accepting applications.)

Once the dust settled, TechCrunch’s team queried top investors in attendance and huddled together to choose our picks from this season. With fewer inane social apps and no-one-needs-this service startups, it was especially tough this time around, but here’s our selection:
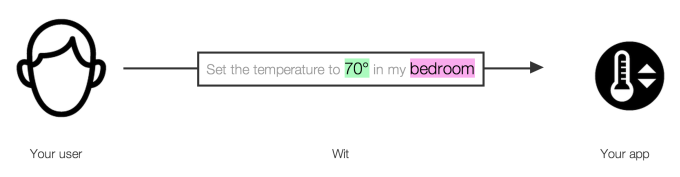
 Wit.ai – Voice Interface API
Wit.ai – Voice Interface API
Voice is how we’ll control devices too small for a keyboard, like watches, earbuds, and much of the “Internet Of Things.” But it’s a ton of work for a developer to build their own voice system, with natural language processing, speech recognition, and other engineering requirements. So Wit.ai has created a voice interface API, and developers can pipe into their app to enable voice command. That could let them offer in-app voice search, hardware control without buttons, and more.
Its co-founder sold his last company to speech tech giant Nuance, and now Wit.ai has 3,000 developer-users like Pebble and Samsung and is growing 29 percent per week. Every app will soon need speech tech, and any startup that can offer an alternative to big providers like Nuance or (maybe) Google will be in a great position for traction or acquisition. Read more from TechCrunch about Wit.ai.
–
 The Dating Ring – Matchmaker-Assisted Online Dating
The Dating Ring – Matchmaker-Assisted Online Dating
“Dating should work like Uber, and with The Dating Ring, it does,” says the startup’s co-founder. Currently, dating online is a big hassle. You sift through profiles or Tinder cards, approve some people, wait for a match, and make chit chat. If you’re lucky, it progresses to a real date, but then your partner might look nothing like your partner.
With The Dating Ring, you apply to join. Pass the first bar and you’ll meet in-person with a Dating Ring matchmaker for five minutes. They’ll assess your style and open the ability to go on group dates with three men and three women (or a group of four for gay users). But unlike Grouper, a matchmaker has ensured you’re more likely to fall for one of your date mates. Users pay $25 for the initial matchmaker meeting and $20 per date. The Dating Ring certainly made a stir when it announced plans to crowdfund planes full of women to be delivered from New York City to lonely San Francisco guys.
The Dating Ring’s revenue is growing 60 percent per month for the last six months, it’s profitable, and 70 percent of users go on a second date. While only $2 billion a year is spent in the space, The Dating Ring wants to grow the pie. It seems reasonable that people would be willing to pay for love…or at least to go on real, match-made dates instead of endlessly browsing profiles online. Read more from TechCrunch about The Dating Ring.
–
It’s crazy that when you’re at your computer, you still have to open your phone to look at push notifications. Pushbullet syncs them so you can respond on the device you’re currently using, including the web thanks to a Chrome/Firefox extension. You can even send files back and forth between your phone and computer. But Pushbullet also lets you turn changes on websites and more into push notifications, even if a site doesn’t have a mobile app. For example, you could ask to get an alert the next time Nike puts a new line of shoe on sale.
Pushbullet is now handling 10 million notifications a day for 100,000 weekly users and 60,000 daily users. Push is quickly becoming the most powerful way to reach people and is eating email’s lunch. Pushbullet could hit the bullseye by enhancing the standard and bringing it to more devices and sites. Read more from TechCrunch about Pushbullet.

–
AirHelp: Stick it to the airline 

AirHelp wants to help fliers get compensation that they are legally entitled to after an airline screws up and is late, or cancels their flight. The total dollar amount this sums to each year is $16 billion. And you can go back three years, meaning that there is another $48 billion potentially sitting there.
AirHelp handles the details. You put in your flight number, and if you can get paid, they’ll handle it. The company takes a one-fourth cut if it gets you money back. Not a bad business model unless you are an airline.
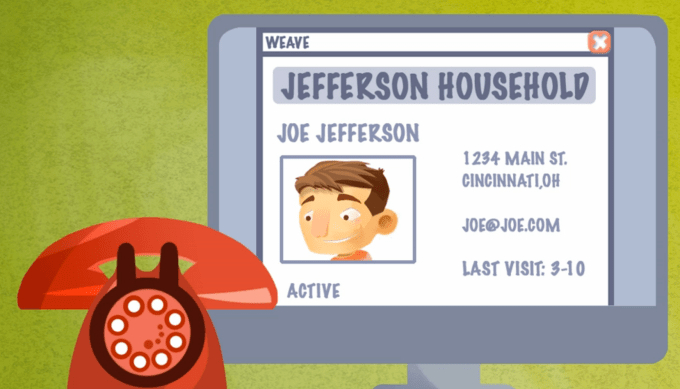
Weave: Integrated Phone/Software Systems For Doctors

Weave is a telephone service that better connects patients and their medical providers. Going to the dentist is roughly as fun as, well, going to the dentist. The company wants to make that better by helping dentists keep track of their patient information, and needs, integrating that into their communications system. When you call, the receptionist instantly sees your profile connected to your phone number. This way they don’t have to put you on hold, they can instantly see info about your past visits, and they can even spot revenue opportunities like that your spouse hasn’t had a teeth cleaning in two years (eww).
Before Y Combinator, Weave had yearly recurring revenue of $790,000. Post Y Combinator, that figure is now $1.8 million, up 38 percent per month during the period. Weave picked dentists to start because they are wealthy and low on regulation. The product will scale into other health verticals. Weave charges $300 per month per location for its service. There are 190,000 dental offices in North America, indicating that its addressable market is quite large. And Weave is determined to scale its system to other health verticals, making medical care better and friendlier across the board. Learn more about Weave on TechCrunch.
–
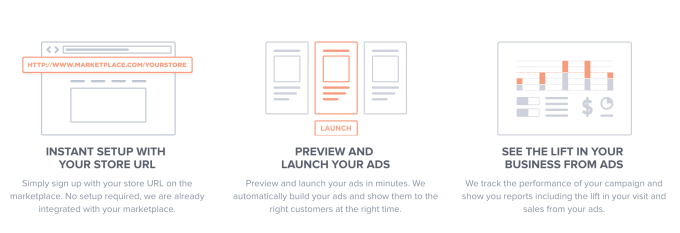
 Boostable: Advertising Help For Marketplace Sellers
Boostable: Advertising Help For Marketplace Sellers
There are 30 million sellers on marketplaces like Airbnb and Etsy, and they all want more sales. Bettable makes it dead-simple for them to run ads promoting their apartment for rent, or homemade handicraft. Sellers just sign up and send Boostable the URL of their listing or item, select their budget, and Boostable runs efficient, A/B-tested ad campaigns on Facebook and soon Google using advanced retargeting to show them to the right people.
And since each sale also earns the marketplaces money, they’re happy to connect Boostable to their sellers. Airbnb has already partnered with the startup. With its current deals, Boostable could reach 500,000 sellers. If it can convince advertising novices they need to spend money to make money, Boostable could pull in enough small ad contracts to see huge revenue.
–
Kimono Labs: Web Scraping In One Click

Kimono turns websites into APIs. What that means is that you can point Kimono at a website, set parameters, and scrape data from it. Think of it like building a small Google just for your needs aimed at one website.
So far 20,000 devs have signed up to use the service, a figure that is growing 15 percent per week. In its short life of around 10 weeks, Kimono claims to have helped triple the number of public APIs online. I’m honestly interested to see what people could do with Kimono, TechCrunch, and CrunchBase data. Data becomes much more valuable when it’s structured. Read more from TechCrunch about Kimono Labs.
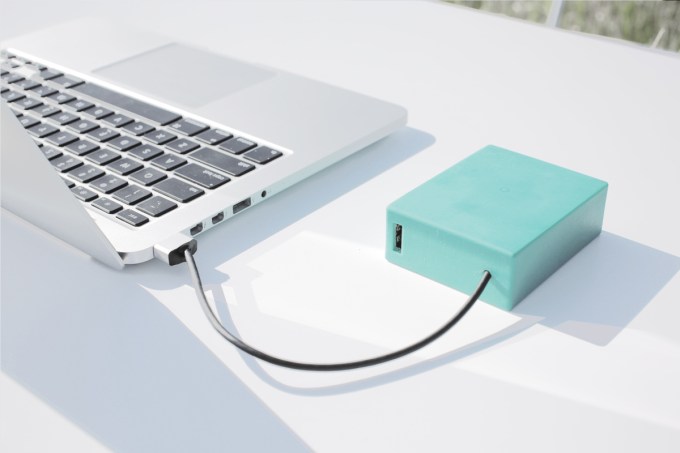
BatteryOS: Better battery-life management 

According to BatteryOS, if you charge a battery to 100 percent, it rapidly degrades the battery itself. After many cycles, batteries’ capacity declines. With BatteryOS, the company claims you will be able to charge your batteries to full capacity and not suffer that degradation.
The company claims that if the Chevy Volt used BatteryOS, it would have twice the range, and last 8 years longer. The company did not explain how its product works, but did allude to having orders for units in the tens of thousands. Learn more about BatteryOS from TechCrunch’s coverage here.
–
 Honorable Mention
Honorable Mention
Noora Health: Healthcare Training For Families
Noora Health trains families to take care of their kin after they return from the hospital. For families living, say, more than one hundred miles from professional medical care, basic healthcare knowledge could be a scarcity. Imagine having a child with a serious heart condition and stressing that you might do something wrong with their medication, care, or diet that could land them back in the hospital or worse? Noora Health gives families training that can be taken back to their homes, leading to healthier outpatients.
They don’t go back as nurses, but the training that individuals receive from Noora Health can reduce complications by 36 percent. The non-profit estimates that its training thus far has saved 124 lives. The company has trained 7,000 families so far.
The company is selling its product to hospitals in the U.S. and using those funds to pay for its work in other places. The company told gathered investors and press that it is building something that is not dependent on donor dollars. It’s a smart model that makes Noora feel more like a startup than a charity. For a deeper look at Noora Health, check out TechCrunch’s past coverage.

Source: Source









